BADBOX 2.0 Case Study: Google’s July 2025 Lawsuit Against the Botnet Infecting 10 Million Residential Android Open-Source IoT Devices

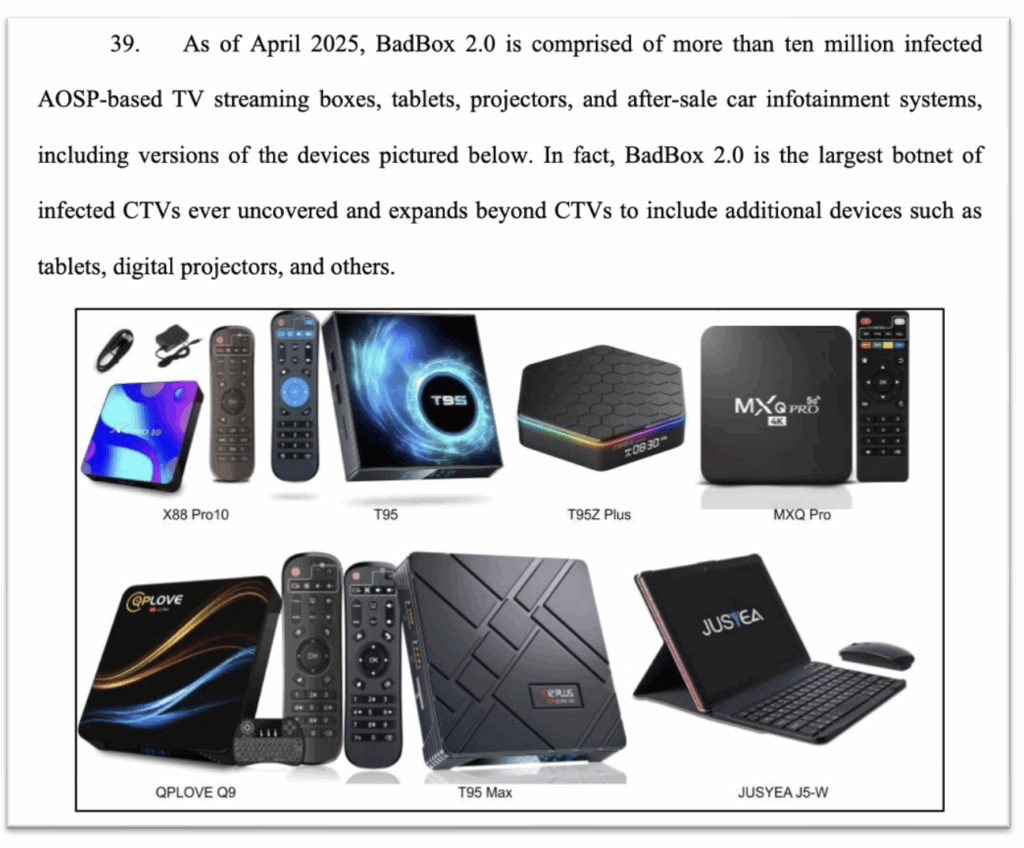
On July 11th, 2025, Google made headlines by taking legal action against the BADBOX 2.0 botnet, a sophisticated, global network of over 10 million compromised IoT devices.
Through collaboration between Google, HUMAN Security, Trend Micro, and the Shadowserver Foundation, security researchers uncovered BADBOX 2.0, the largest known botnet of Internet-connected TVs to date with over 10 million consumer IoT devices compromised in their network. Their federal lawsuit in New York federal court represents notable legal action against organized cybercriminals that operate on a global scale.
Executive Summary
The BADBOX 2.0 investigation reflects how the threat actors have shifted their targets and tactics following the original BADBOX disruption of 2023.
Targeting mainly low-cost, uncertified Android Open-Source Project (AOSP) devices embedded with backdoors, the attackers used these devices to carry out a variety of fraud schemes, including:
- Residential proxy services: selling access to the device’s IP address without the user’s permission
- Fraudulent ads as hidden ad units: using built-in content apps to render hidden ads
- Deceitful ads as hidden WebViews: launching hidden browser windows that navigate to a collection of game sites owned by the threat actors
- Click fraud: navigating an infected device to a low-quality domain and clicking on an ad present on the page
Researchers also observed payloads capable of programmatically creating accounts, collecting sensitive data, and executing arbitrary code. Multiple criminal enterprises groups worked together to deploy malicious payloads on an international scale to extend the botnet’s capabilities.
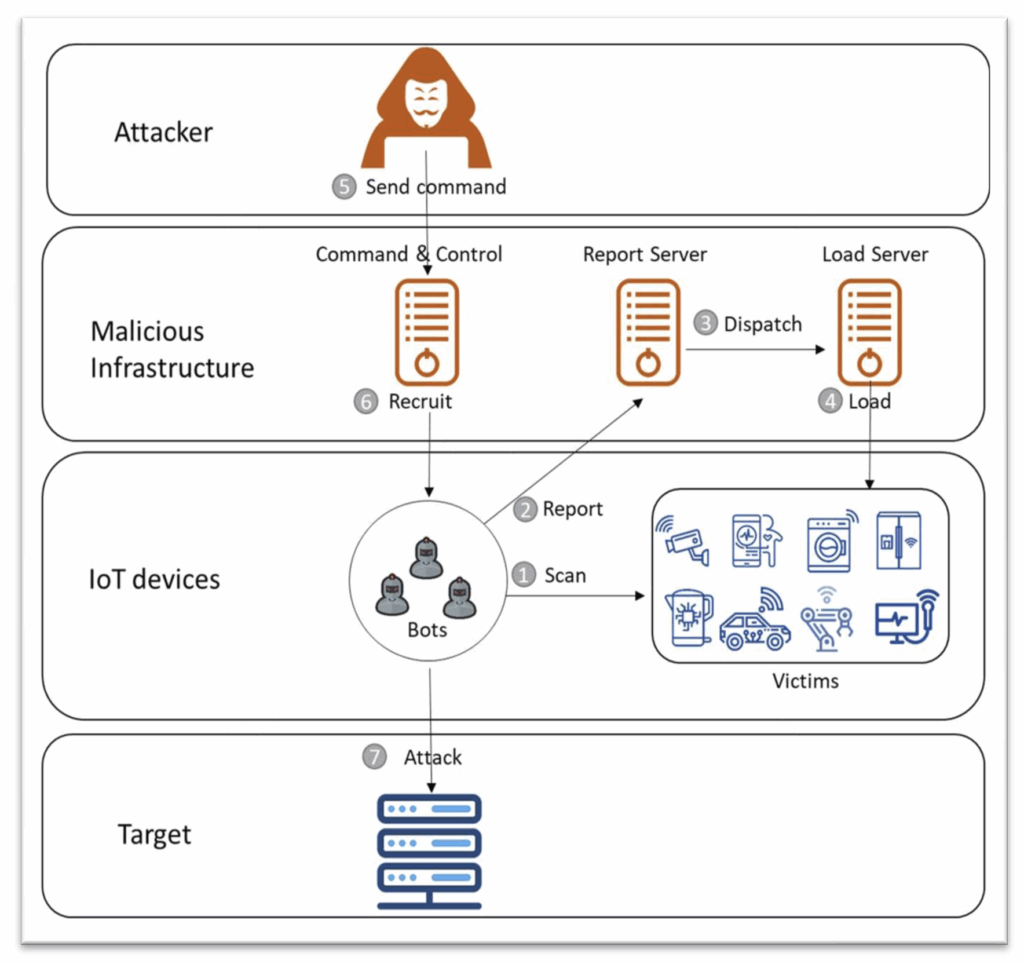
While security researchers observed the threat actors pushing payloads to the device to implement these fraud schemes, attackers are not just limited to these four types of fraud. The threat actors behind BOTNET 2.0 have the ability to push any functionality they want to the device by loading and executing an APK file of their choosing, or by requesting the device to execute arbitrary code. For instance, security researchers at Trend Micro who collaborated on this investigation with HUMAN observed multiple threat actor groups (e.g., PeachPit, Lemon Group) deploying payloads to automatically create online marketplace accounts, collect personal information from infected IoT devices, and more.
Similar to the 2023 BADBOX operation, devices infected by BADBOX 2.0 are off-brand low-cost consumer devices built or assembled in China and shipped worldwide. When security researchers confirmed the presence of the backdoors, fortunately preliminary findings were shared with security representatives capable of digging further into the various fraud schemes perpetrated by the threat actors through the boxes.
Let’s Study! BADBOX 2.0 IoT Backdoor Distribution
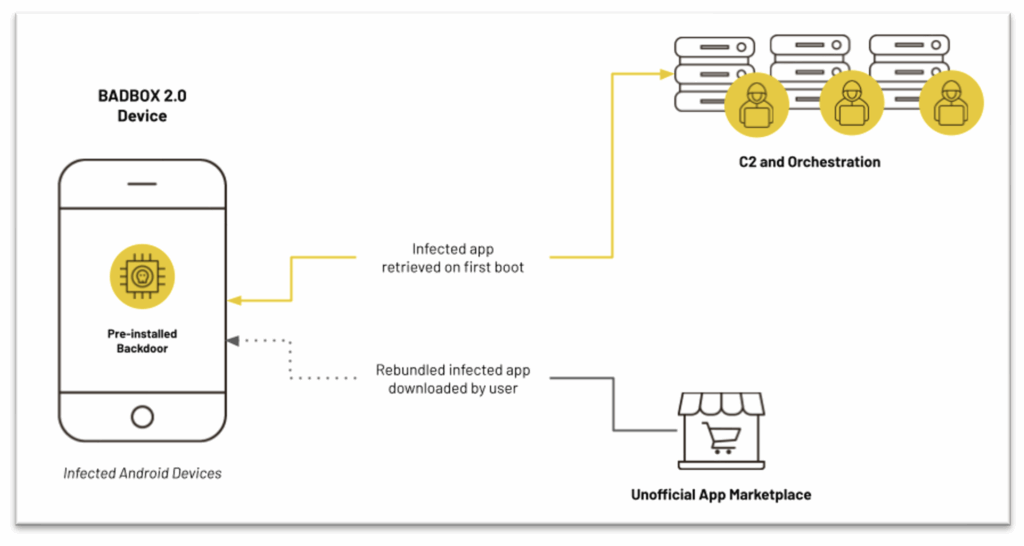
Researchers identified three main methods of backdoor installation underpinning BADBOX 2.0:
- Backdoor Installation 1: pre-installed on infected Android Open Source Project (AOSP) devices, in a similar fashion to the primary 2023 BADBOX backdoor
- Backdoor Installation 2: orchestrated from a command-and-control (C2) server contacted by the device on first boot
- Backdoor Installation 3: installed as an app from an unofficial app marketplace by unsuspecting users
However, more dangerous than residential proxy access alone is the combination of attack vectors involving the downstream attacks that a residential proxy access facilitates. Threat actors who purchase residential proxy access often use that access to conduct attacks of their own, as the IP address associated with the attack will be different from the address they’re operating from.

Timeline and Targeting to Backdoor Distribution

As of January 2025, security researchers estimate more than 1 million devices worldwide are infected by BADBOX 2.0. More than a third of the BADBOX 2.0-infected devices observed by the Human Defense Platform are located in Brazil, where low-cost Android Open Source Project devices are particularly popular. Other countries with significant numbers include the United States, Mexico, Argentina, and Colombia. Overall, HUMAN observed BADBOX 2.0-associated traffic coming from 222 countries and territories worldwide:


As featured previously in Zscaler’s Data@Risk report, entertainment and home automation devices frequently route to China and Russia. As studied in Zscaler’s Operational Technology (OT) threat report, 3 billion IoT device transactions from 850+ unique device types were analyzed to reveal that IoT devices from entertainment and home categories like smart TVs, game consoles, set-top boxes, and IP cameras are the primary contributors to traffic headed to China and Russia. While much of this network activity is legitimate, non-malicious traffic, these destinations have high potential for government spying and other highly-motivated data vulnerabilities.
Observed BADBOX 2.0 Attack Vector: Hidden WebViews/H5 Domains
Satori’s security researchers documented a multi-level scheme in which BADBOX 2.0-infected devices leveraged hidden WebViews (imagine: browser windows) and navigated to one of a large number of websites hosting HTML5 games.
Many of these H5 game sites, of which there were hundreds, share the general pattern: a homepage with tiles promoting web-based games, a navigation bar, and not much else.

Clicking through to one of the games reveals a frustrating experience for actual gameplay: in-game ads every few seconds, making gameplay impossible.
The frequency of the ads reinforces two important notes about how the threat actors monetize this scheme:
- CPMs is integral to the scheme. CPM is cost per mille, the price for 1,000 ad renders. CPM for in-game ads can be up to double the price for digital mobile ads, allowing for the app publisher (H5 game site owner) to receive more money per ad.
- There is no expectation for realistic human interaction on these sites, as the gameplay is so frequently interrupted by ads.
This strategy monetized fraudulent ad impressions at higher CPMs (Cost Per Mille) than typical mobile ads — without realistic expectations of human engagement.
Observed BADBOX 2.0 Attack Vector: Decoy Apps
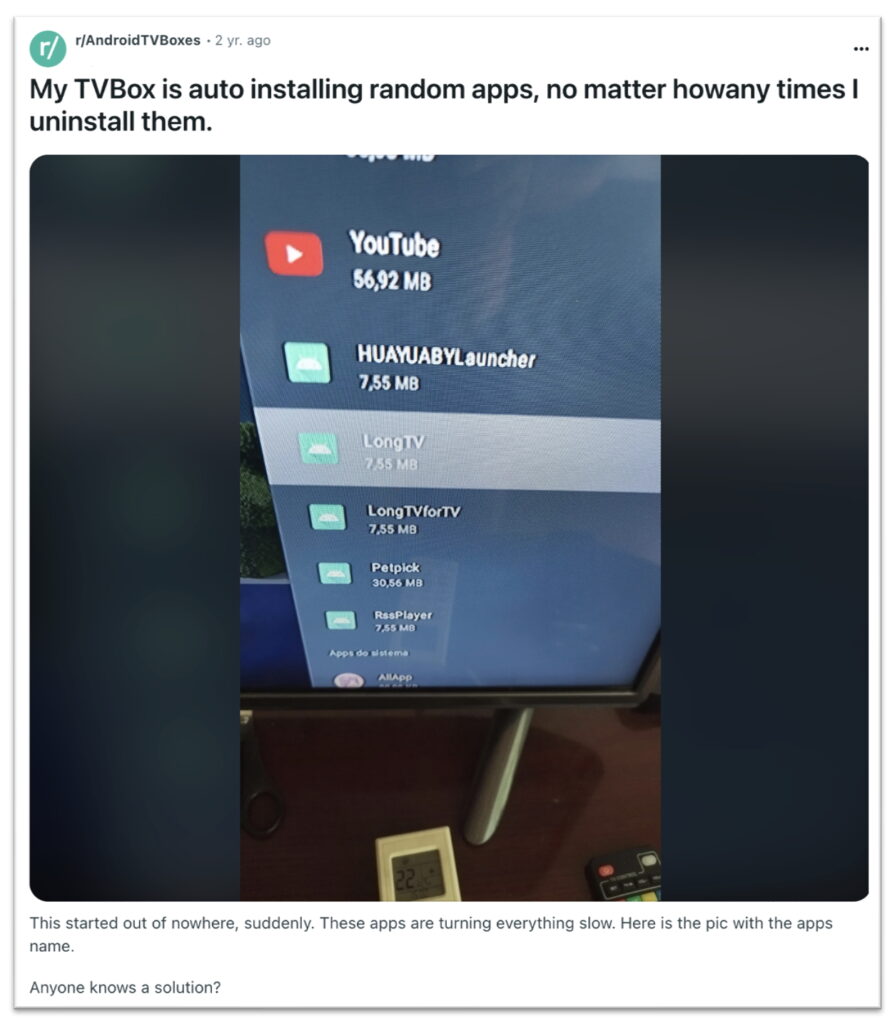
Digital threat actors have “rebundled” and uploaded an extensive collection of publicly available apps to unofficial app marketplaces. These apps have the marketing of well-known, popular apps, but actually are “dupes” and have had the BB2DOOR backdoor installed.
Decoy BADBOX 2.0 apps, for example “Earn Extra Income” and a “Pregnancy Ovulation Calculator,” both published by “Seekiny Studios”, were uploaded to the Google Play Store to make its ad request appear legitimate, a highly profitable attack vector when automated.
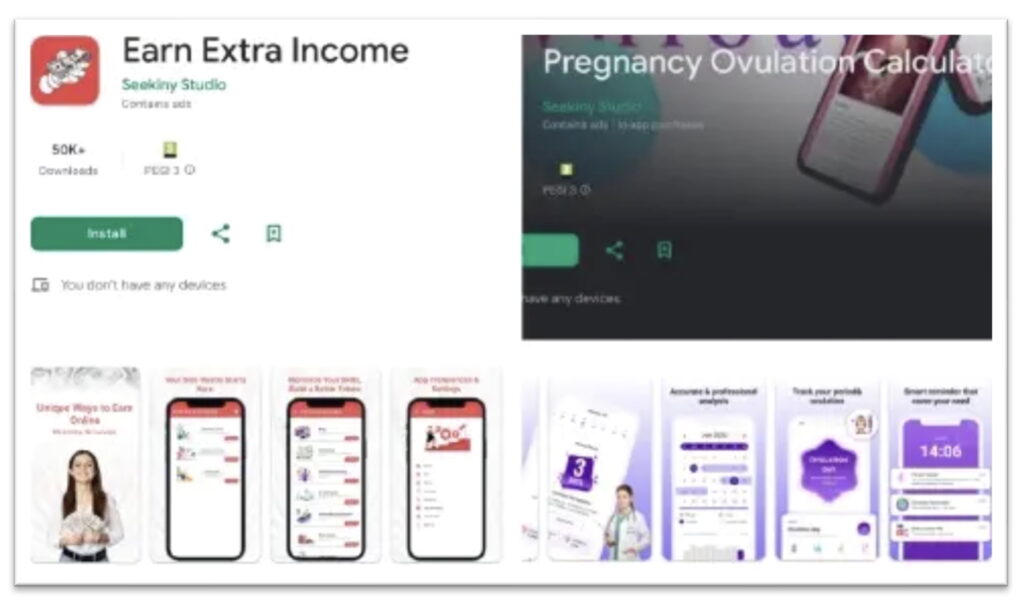
These “decoy” apps hosted in Google Play have thousands of downloads but no reviews. Despite the fact that these are promoted as apps for mobile devices, nearly all the ad traffic that “Earn Extra Income” and “Pregnancy Ovulation Calculator” have generated came from versions of the app located on BadBox 2.0-infected devices. The BadBox 2.0 hidden ads scheme generates billions of fraudulent requests to render ads per week, lining the pockets of criminal enterprise developers.
Indicators of Compromise
A FBI Public Service Announcement addressing the BADBOX 2.0 botnet encourages the general public to examine their home IoT devices for signs of compromise and to disconnect any suspicious devices. Please note that these indicators alone do not confirm malicious activity but should be evaluated in context.
An indicator alone does not accurately determine malicious cyber activity or a crime. The following suspicious activities/indicators do not relate to any individual, group, or business and should be observed in context.
Possible indicators of BADBOX 2.0 botnet activity include:
- The presence of suspicious marketplaces where apps are downloaded.
- Requiring Google Play protect settings to be disabled.
- Generic TV streaming devices advertised as unlocked or capable of accessing free content.
- IoT devices advertised from unrecognizable brands.
- Android devices that are not Play Protect certified. Visit Google’s simple tutorial on checking if your Android device is Play Protect certified.
- Unexplained or suspicious Internet traffic.
Mitigation Strategies
The following mitigation strategies are known effective steps to minimize exposure to unauthorized proxy networks, even at the residential level.
- Maintain awareness and monitor Internet traffic of home networks.
- Assess all IoT devices connected to home networks for suspicious activity.
- Avoid downloading apps from unofficial marketplaces advertising free streaming content.
- Keep all operating systems, software, and firmware up to date. Timely patching is one of the most efficient and cost-effective steps to minimize its exposure to cybersecurity threats. Prioritize patching firewall vulnerabilities and known exploited vulnerabilities in internet-facing systems.
Is My Device Infected?

We investigated IoT devices infected with BADBOX 2.0, taking cues from the independent researchers who initially uncovered this malware. Many of the infected models fall into “families” — sharing the same letters in their names but differing slightly in numbers. These operations evolve quickly, but their naming conventions tend to be repetitive and easily predictable.
If you’re unsure what model you own, check the sticker on the device itself — it’s usually printed there. If not, you can also find the model name on your original receipt or in your order history.
Do you own an Android TV box with one of these names?
-
T95 · AllWinner H616
-
T95Max · AllWinner H618
-
X12-Plus · RockChip 3328
-
X88-Pro-10 · RockChip 3328
…and does device contain either of the following filepaths:
-
A folder named:
/data/system/Corejava -
Or a file named:
/data/system/shared_prefs/open_preference.xml
If so, your IoT device is infected with BADBOX 2.0 malware. It continuously attempts to connect to a command-and-control (C2) server to upload “telemetry” and receive remote commands — all without your knowledge or consent.
This malware comes preinstalled, directly from the merchant you purchased it from.
Incident Reporting
If you believe your devices have been compromised by the BADBOX 2.0 botnet, please report the incident immediately to the FBI’s Internet Crime Complaint Center (IC3) at www.ic3.gov.
Any opinions, findings, and conclusions or recommendations expressed in this material are those of the author and do not necessarily reflect the views of the National Science Foundation.
This article was written by a student researcher at ICDC. Interested in building your defenses against modern digital threats? Check out our current IoT course offerings at the Cybersecurity & Networking program at Claremont Graduate University’s Center for Information Systems & Technology. →
Share